
We're RETVRNing, everyone.

I really don't know how to feel about this one.
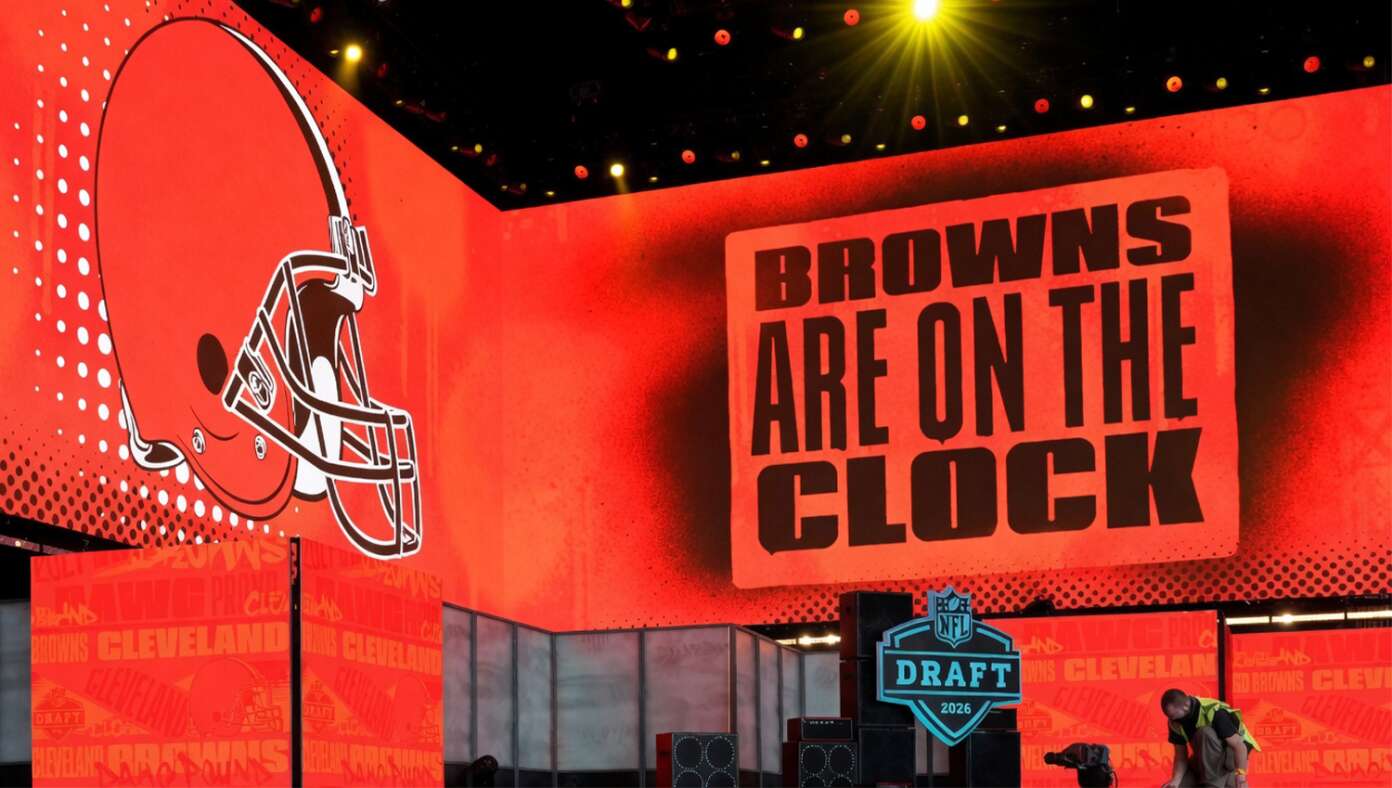
U.S. — In what has become one of America's most cherished annual traditions, a giddy nation will gather around its televisions this evening to see which young man will have his career killed by the Cleveland Browns.